Azure DevOps
Supported on Enterprise plans.
Available via the Web app.
Site admins can sync Git repositories hosted on Azure DevOps with Sourcegraph so that users can search and navigate the repositories.
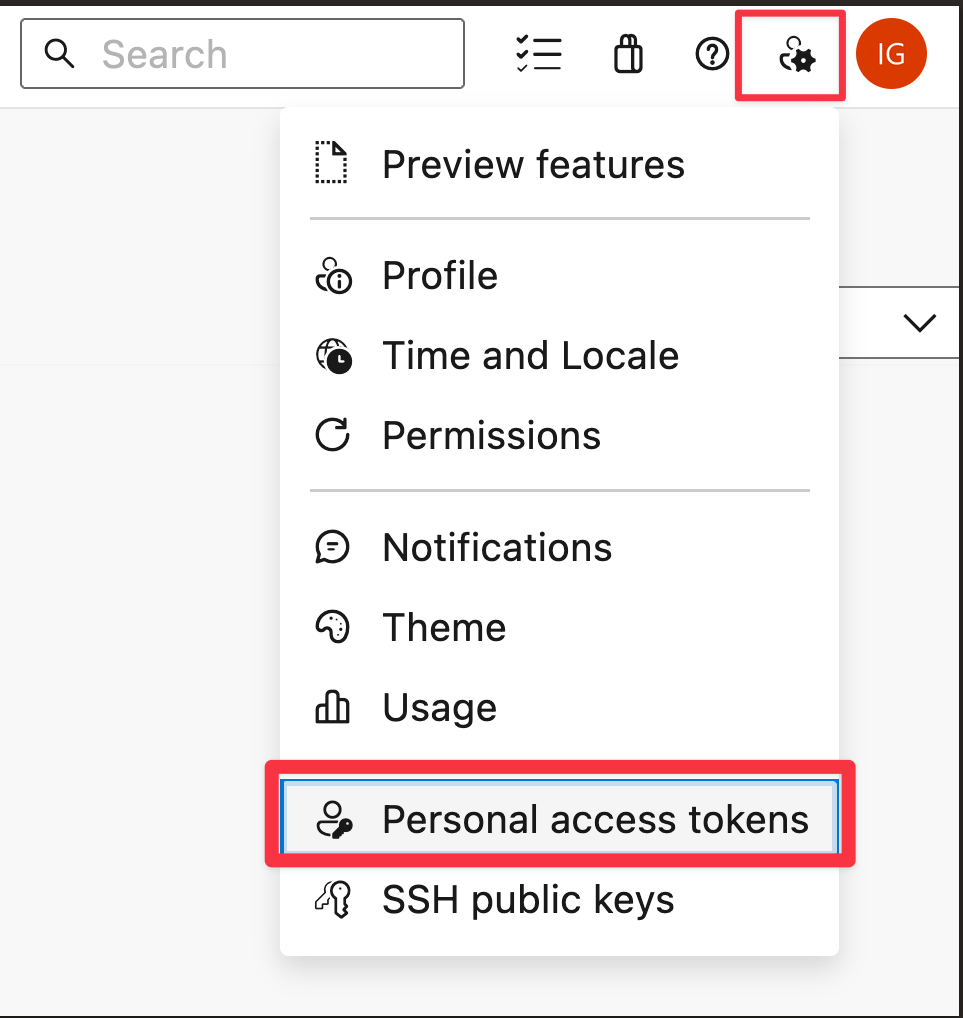
To connect Azure DevOps to Sourcegraph, create a personal access token from your user settings page by following the below steps:
- Navigate to the
Personal Access Tokenspage from the user settings.
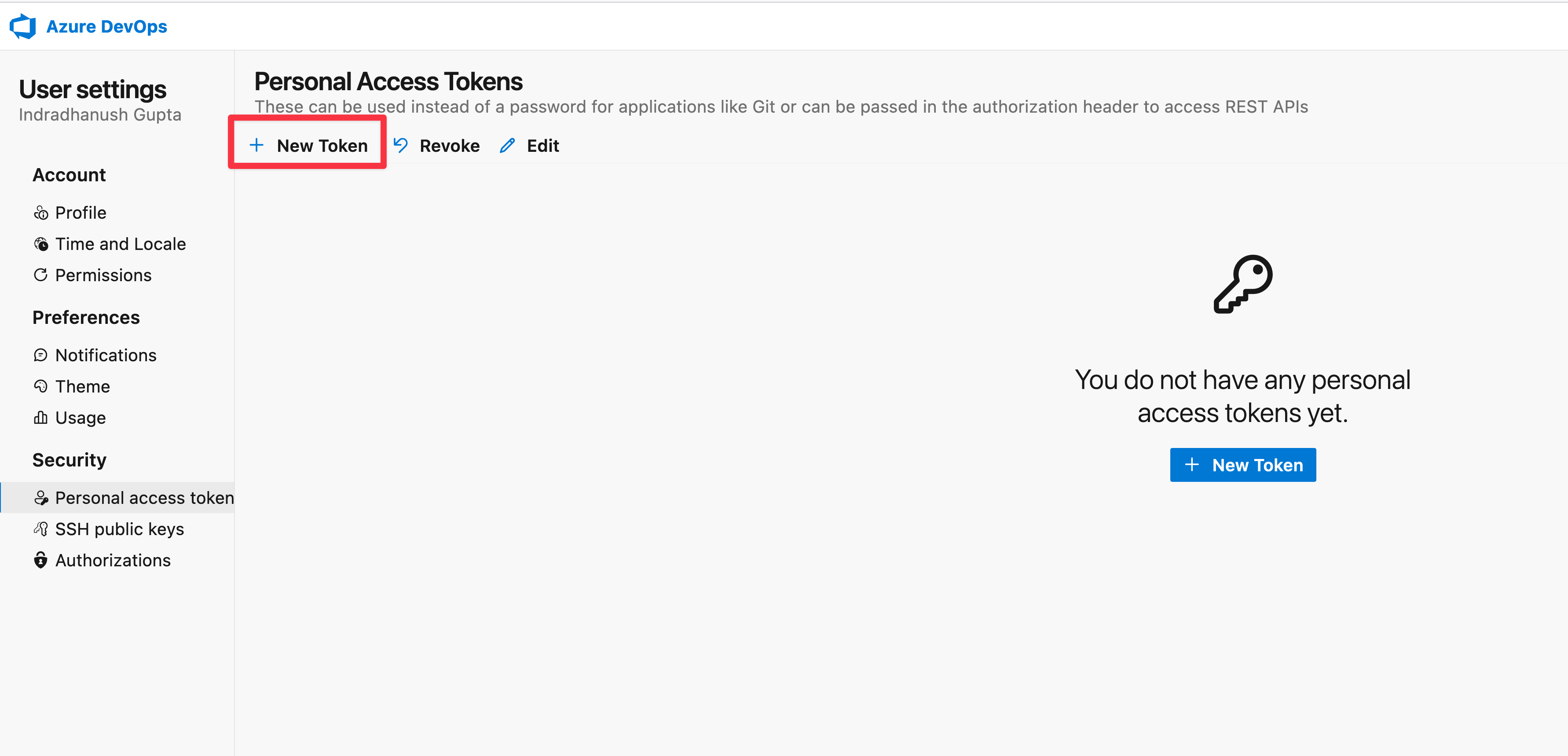
- Click on
New Token.
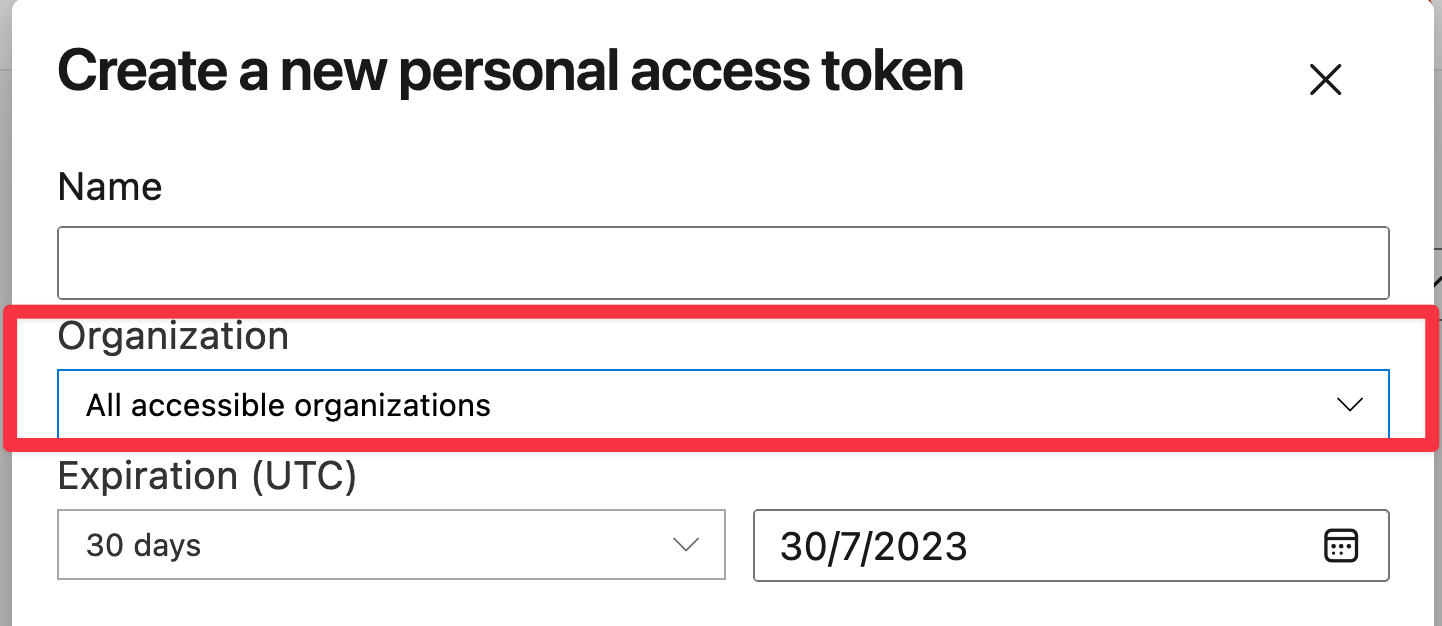
- Under the
Organizationmenu, selectAll accessible organizationsto allow access to all organizations. This is required to be able to perform connection checks from the code host page and to sync repositories from multiple organizations. Alternatively, site admins may also create a unique user that has access to only the selective organizations that they would like to sync with Sourcegraph. However the token being created must have access toAll accessible organizationsas shown below.
-
Select the following scopes:
- Code (Read)
- Project and Team
- User Profile
Next, configure the code host connection by following the next steps:
-
Go to Site admin > Manage code hosts > Add repositories.
-
Select Azure DevOps.
-
Provide a configuration for the Azure DevOps code host connection. Here is an example configuration:
JSON{ "url": "https://dev.azure.com/", "username": "<admin username>", "token": "<admin token>", "projects": ["org1/project1"], "orgs": ["org2"] } -
Select Add repositories.
Repository syncing
Currently, all repositories belonging to the configured organizations/projects will be synced.
In addition, you may exclude one or more repositories by setting the exclude field in the code host connection.
HTTPS cloning
Sourcegraph clones repositories from Azure DevOps via HTTP(S), using the username and token required fields you provide in the configuration.
Configuration
Azure DevOps connections support the following configuration options, which are specified in the JSON editor in the site admin "Manage code hosts" area.
admin/code_hosts/azuredevops.schema.json
JSON// Authentication alternatives: token OR windowsPassword { // A flag to enforce Azure DevOps repository access permissions "enforcePermissions": false, // A list of repositories to never mirror from Azure DevOps Services. // Other example values: // - [ // { // "name": "myorg/myproject/myrepo" // } // ] // - [ // { // "name": "myorg/myproject/myrepo" // }, // { // "name": "myorg/myproject/myotherrepo" // }, // { // "pattern": "^topsecretproject/.*" // } // ] "exclude": null, // SSH cipher to use when cloning via SSH. Must be a valid choice from `ssh -Q cipher`. "gitSSHCipher": null, // SSH keys to use when cloning Git repo. "gitSSHCredential": null, // The type of Git URLs to use for cloning and fetching Git repositories. // If "http", Sourcegraph will access repositories using Git URLs of the form http(s)://dev.azure.com/myrepo.git. // If "ssh", Sourcegraph will access repositories using Git URLs of the form git@ssh.dev.azure.com:v3/myrepo. See the documentation for how to provide SSH private keys and known_hosts: https://sourcegraph.com/docs/admin/repo/auth. // Valid options: "http", "ssh" "gitURLType": "http", // The maximum number of repos that will be deleted per sync. A value of 0 or less indicates no maximum. "maxDeletions": 0, // An array of organization names identifying Azure DevOps organizations whose repositories should be mirrored on Sourcegraph. // Other example values: // - [ // "name" // ] // - [ // "kubernetes", // "golang", // "facebook" // ] "orgs": null, // An array of projects "org/project" strings specifying which Azure DevOps projects' repositories should be mirrored on Sourcegraph. // Other example values: // - [ // "org/project" // ] "projects": null, // Rate limit applied when making background API requests. "rateLimit": { "enabled": false, "requestsPerHour": 0 }, // The pattern used to generate the corresponding Sourcegraph repository name for a Azure DevOps repository. // - "{host}" is replaced with the Azure DevOps URL's host (such as dev.azure.com) // - "{orgName}" is replaced with the repository's parent projects owning organization (or collection on DevOps server) // - "{projectName}" is replaced with the repository's parent project // - "{repositoryName}" is replaced with the repository's name. // For example, if your Azure DevOps is https://dev.azure.com and your Sourcegraph is https://src.example.com, then a repositoryPathPattern of "{host}/{orgName}/{projectName}/{repositoryName}" would mean that a Azure DevOps repository at https://dev.azure.com/MYORG/MYPROJECT/MYREPO is available on Sourcegraph at https://src.example.com/dev.azure.com/MYORG/MYPROJECT/MYREPO. // It is important that the Sourcegraph repository name generated with this pattern be unique to this code host. If different code hosts generate repository names that collide, Sourcegraph's behavior is undefined. // Other example values: // - "{projectName}/{repositoryName}" "repositoryPathPattern": "{host}/{orgName}/{projectName}/{repositoryName}", // The Personal Access Token associated with the Azure DevOps username used for authentication. "token": null, // REQUIRED: // URL for Azure DevOps Services, set to https://dev.azure.com. // Other example values: // - "https://dev.azure.com" "url": null, // REQUIRED: // A username for authentication with the Azure DevOps code host. Typically an email address when connect to Azure DevOps Services (cloud) and a domain\username when connecting to Azure DevOp Server (onPrem) "username": null, // Windows account password (Azure Devops Server OnPrem Only): This is needed to clone the repo, the Token will be used for REST API calls "windowsPassword": null }
Webhooks
Please consult this page in order to configure webhooks.
Permissions syncing
User-level permissions syncing is supported for Azure DevOps code host connections. Here is the list of prerequisites:
-
Configure Azure DevOps as an OAuth provider by consulting this page
-
Next verify that users can now sign up / login to your Sourcegraph instance with your Azure DevOps OAuth provider
-
Set the following in your Azure DevOps code host connection:
JSON{ // ... "enforcePermissions": true } -
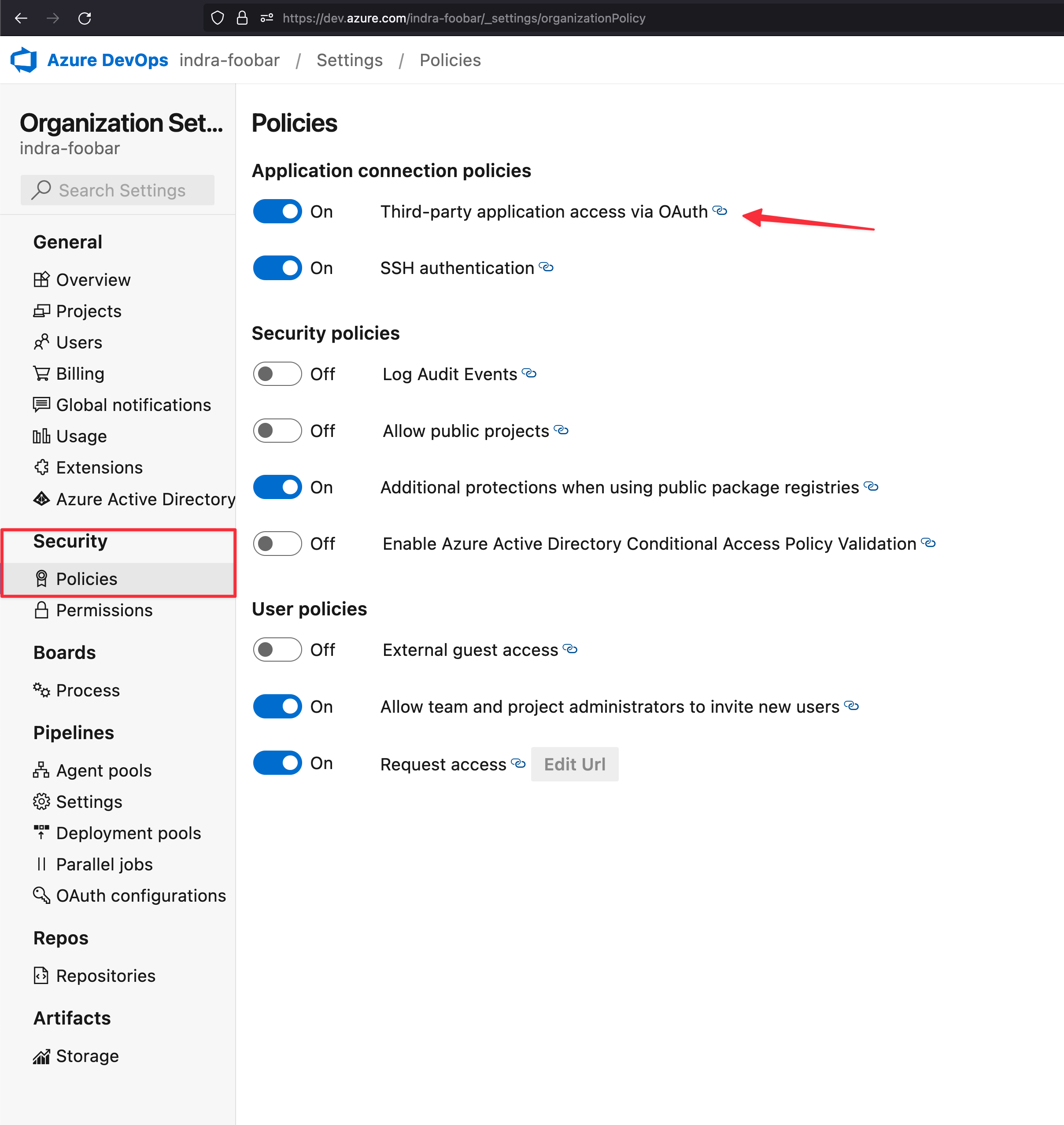
For each Azure DevOps organization that is part of the
orgsorprojectslist in the code host configuration, enable Third-party application access via OAuth from Organization settings > Security > Policies
NOTE: We do not support preemptive permissions syncing at this point. Once a user signs up / logins to Sourcegraph with their Azure DevOps account, Sourcegraph uses the authenticated
access_tokento calculate permissions by listing the organizations and projects that the user has access to. As a result, immediately after signing up user level permissions may not be 100% up to date. Users are advised to wait for an initial permissions sync to complete, whose status they may check from thePermissionstab under their account settings page. Alternatively they may also trigger a permissions sync for their account from the same page.
Since permissions are already enforced by setting enforcePermission in the code host configuration, even though user permissions may not have synced completely, users will not have access to any repositories that they cannot access on Azure DevOps. As the user permissions sync progresses and eventually completes, they will be able to access the complete set of repositories on Sourcegraph that they can already access on Azure DevOps.
Rate limits
When Sourcegraph hits a rate limit imposed by Azure DevOps, Sourcegraph waits the appropriate amount of time specified by the code host before retrying the request. You can read more about how Azure DevOps imposes rate limits here.